Cybersecurity can be a complex and confusing topic, especially if you aren’t a security researcher or work in IT. However, it’s not something you can afford to ignore—especially if you run a small or medium-sized business.
As cyberattacks and data breaches become more common and more costly, it’s more important than ever for companies to continually assess and improve their security posture. Two critical concepts to understand are zero-day vulnerabilities and zero trust access.
If you’re concerned that your business may be vulnerable to cybersecurity attacks, please reach out to the team of experienced cybersecurity professionals at Verdant TCS. We’d be more than happy to help.
WHAT IS A ZERO-DAY VULNERABILITY?
In simple terms, a zero-day vulnerability is any security flaw in software that is either unknown to the developer or vendor of the software, or has been discovered, but no official patch exists yet.
The reality is that no software is 100% secure—at least not forever. Software developers and security researchers analyze and identify emerging cyber threats, and continuously update their systems to fix those flaws and security vulnerabilities—ideally before those flaws are discovered and exploited by cybercriminals. However, with complex software, zero-day vulnerabilities sometimes aren’t discovered (by security professionals or by hackers) for months or even years after the software is released.
In essence, it’s a race between the good guys and the bad guys to find flaws in the code, and unfortunately the hackers sometimes identify software vulnerabilities before a developer does. If malicious actors can use the flaw to gain access, it’s called a zero-day exploit. If they then are able to use that exploit to deploy malware and carry out a cyberattack—freezing accounts, remotely accessing machines, identity theft or stealing confidential data, etc.—it’s called a zero-day attack.
Zero-day attacks can be especially dangerous and destructive since the attack catches the developer flat-footed. The hackers attack before they even know there is a vulnerability, and businesses have no existing security patches or any other solutions to protect their systems.
Hence the use of the term “zero day.” Once discovered, cybersecurity experts have “zero days” left to fix the security flaw. And because these are unknown threats, if the malicious actors are stealthy, they could take advantage of the exploit undetected for an extended period before security experts either discover the attack or find a way to fix it.
RELATED: 5 Cybersecurity Threats to Monitor in 2021
WHAT IS ZERO TRUST ACCESS?
Zero trust access—also known as zero trust security—is another cybersecurity term you might have seen in the news recently. Although it isn’t directly related to zero-day vulnerabilities, exploits, or attacks, it is an important concept for businesses and employees to understand and can help reduce the risk of zero-day threats.
Zero trust access is a cybersecurity strategy or framework that requires all users to not only be authenticated and authorized to access networks, but also continuously validated in order to retain that access and connect with other applications, resources, or data. In other words, locks are set up not just between the corporate network and the outside world, but also within the network itself. Not only is it harder for an attacker to get in the front door, but it can also significantly limit the amount of damage that can be caused by a single breach.
Essentially, the motto is “never trust, always verify.” Any network connection, internal or external, should always be considered a potential threat.
Zero Trust vs. Perimeter Defense Strategies
Many organizations still employ an outdated “perimeter” or “castle and moat” cybersecurity strategy. Yes, these companies might be using multifactor authentication, firewalls, antivirus software, and other important cybersecurity technologies and strategies. But with a perimeter defense strategy, once a person gains access to the network and operating systems, their credentials are not checked again. They’re assumed to be trustworthy and given extensive, mostly unrestricted access to internal systems.
As networks become more complex and require more interconnectivity, though, this way of thinking is no longer secure. Today’s corporate data centers are not isolated entities. Some applications are on-premises, others are in the cloud, and users may need to access networks from a wide variety of devices and locations. Eventually, the “perimeter” becomes incredibly hard to even define—and it’s much less secure.
The Colonial Pipeline hack is a great example of why a robust zero trust security model is so critical for today’s organizations. All the hackers had was a single password to an obsolete (but still active) VPN (Virtual Private Network). That one-time authentication check from a long-forgotten endpoint was all they needed to steal a trove of confidential data, compromise Colonial Pipeline’s billing system, shut down the pipeline for days, and trigger fuel shortages and panic buying across the Southeast.
PROTECT YOURSELF FROM ZERO-DAY ATTACKS AND OTHER VULNERABILITIES
Cybersecurity isn’t easy. It would be much simpler for everyone if “perimeter defenses” and a “set it and forget it” mindset still cut it in 2021.
But that’s not the world we live in—and when you read that the average cost of a data breach is over $3 million, and 60% of small companies are out of business within six months of an attack, it becomes clear that you can’t afford to fall behind. Complacency puts your company, the livelihoods of yourself and your employees, and the security of your customers and vendors at risk.
Here are some simple tips that can help protect your organization:
- Keep your operating systems, software, and other resources up to date. As zero-day vulnerabilities are discovered by developers, they are patched via regular security updates. If you aren’t installing the patches, you are at greater risk of being exploited.
- Avoid installing unnecessary applications. In the past, hackers have used zero-day exploits in common software programs like Microsoft Word, Zoom, and others to remotely compromise devices. The more software you have, the greater the number of potential vulnerabilities. Don’t use what you don’t need.
- Invest in cybersecurity training. If a hacker can trick a trusted user into inadvertently providing access—for example, through a phishing attack—they can do real damage. Make sure your employees know how to spot the risks.
- Use a multilayered cybersecurity approach. This is an essential part of any no trust strategy. More layers mean more protection. Examples include multifactor authentication, firewalls, email filtering, machine learning and AI (Artificial Intelligence) threat detection, multiple data backups, and more. It will take time to build a strategy that works for your business, but it’s worth the effort.
RELATED: Ransomware Trends Are Getting Worse: Here’s How to Protect Yourself
VERDANT TCS CAN HELP YOU DEFEND YOUR NETWORK
Verdant TCS was founded to help organizations of all sizes plan, implement, monitor, and support multilayered cybersecurity strategies.
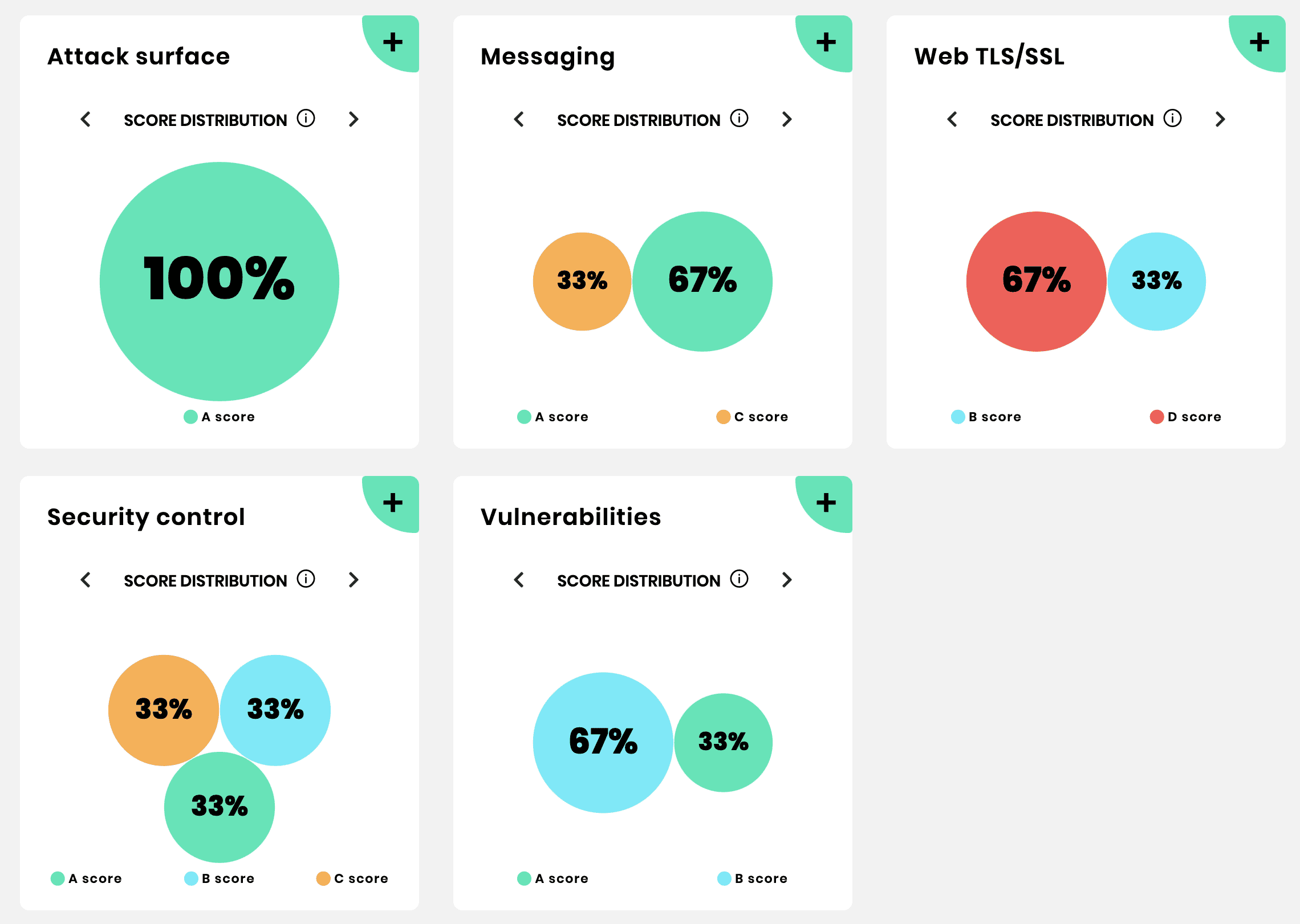
We’ve also partnered with global cybersecurity leader Almond to offer vAlmond, a custom-designed platform that allows users to proactively monitor and improve their daily security rating. Your business can close gaps faster, identify vulnerabilities sooner, keep an eye on multiple software vendors throughout your supply chain, and compare your cybersecurity posture to peers in your industry thanks to vAlmond’s easy-to use dashboard.
We know that many small and medium-sized business don’t have the time, staffing, experience, or budget to stay current with cybersecurity trends. That’s why partnering with the right security partner often makes a significant difference. Verdant TCS can help you meet your security needs, so that your internal team can focus on day-to-day operations and serving your customers.
For more information about our services or to request a vAlmond demo, please call 616-210-1760 or fill out this short form.